Michal Ruda
It’s been a positive experience working with TeskaLabs. We needed to implement application security into our POS application very quickly, and we operate this service for our customers in a secure way thanks to TeskaLabs.
In April 2016, the Czech government passed EET. This new law impacts all businesses and entrepreneurs who accept customers payments. Businesses in all fields, such as hotels, restaurants, shops, wholesalers, transport providers, craftsmen, etc., need to connect to the Czech government’s EET systems digitally and provide electronic evidence of sales in real time. The law will take effect in four waves, with each wave targeting different sectors.Companies in the first initial wave must start reporting to EET systems by the end of 2016; by 2018, every group will be compliant. With numerous types and sizes of business joining the system, O2, the largest integrated telecommunications provider in the Czech market, observed that many would require assistance in adhering to this law while also maintaining data security.
The outcome? eKasa, O2’s new secure, scalable POS application and service utilizing TeskaLabs technology.
O2
Czech Republic a.s.
O2 is the largest integrated telecommunications provider in the Czech market. At present, the company operates close to 8 million mobile and fixed accesses, which ranks it among the market leaders in fully converged services in Europe.
In 2012-2013, O2 completely altered the landscape of the Czech telecommunications playing field and became the first operator in the country to open its network to virtual operators while also revolutionizing the market with its unlimited free tariffs.

Michal Ruda
It’s been a positive experience working with TeskaLabs. We needed to implement application security into our POS application very quickly, and we operate this service for our customers in a secure way thanks to TeskaLabs.
Where there is POS data, there will be cyber attacks. To protect O2’s clients against cybercriminals looking for vulnerabilities to exploit, it was vital that the eKasa information system be protected against and stay resilient to cyber attacks.
Because the EET law impacts almost every business and entrepreneur in the Czech Republic, there will be roughly 10 billion business transactions per year and 4,000 transactions per second during its peak period. Hence, eKasa is prepared to handle massive loads of data quickly without lagging.
O2’s clients trust eKasa to keep their data safe. O2 must operate this large system in a controlled manner, by detecting threats, keeping visibility of security incidents and providing real-time response to any problems.
Source: FireEye


Radek Žert
Partnering with TeskaLabs was a very good decision for us. TeskaLabs' security solution makes things easy for both our project and application development teams. They can focus on delivery of the project and developing the application without being burden with the implementation of application security measures.
O2 IT Services chose TeskaLabs as their application security provider to work on this project with their in-house team and 3rd-party application developers. With TeskaLabs’ security experts on board and TeskaLabs’ application security platform, SeaCat, at their disposal, security was seamless and baked into the eKasa solution from the beginning, at the design and development stages.
"TeskaLab’s SeaCat ensures that every electronic recording of sales is transmitted via a secure, encrypted communication channel, preventing any sensitive information from being accessed, modified or deleted by unauthorized parties who intend to cause harm and/or disrupt the business," says Jiri Kohout, VP of Application Security.
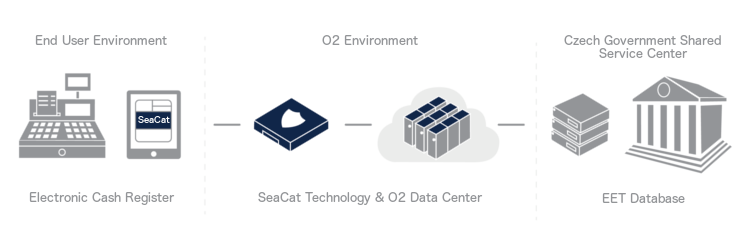
Figure 1. eKasa’s architecture
Due to the expected high data load that will be transmitted from a large number of POS devices, it’s essential that the eKasa system is prepared to handle this enormous load. If eKasa was not adequately prepared for the load, it would fail during operation, disrupting the business of O2 and also the business of O2's customers – including business operational data and backups. To guard against system overload, SeaCat technology serves this number of clients using redundant appliances with a vast performance reserve. Thanks to SeaCat’s ability to achieve massive scale and its capability to process a huge number of concurrent connections, O2 can offer their POS solution and service via the eKasa system to their large existing client base as well as new customers.
SeaCat integrates with the O2 IT Services' Security Expert Center, allowing security officers to monitor application-related activities and have full control over application security. Moreover, O2 has added a new capability: They can provide real-time incident responses with support from TeskaLabs.
 Figure 2. O2 IT Services' Security Expert Center
Figure 2. O2 IT Services' Security Expert Center
Working with TeskaLabs’ security experts and having a proven application security solution at the start of the project allowed O2 to focus their resources. For example, it gave them time to implement eKasa as an integral part of their product portfolio in the Czech Republic. In addition, the budget to build and maintain these appliances was negligible. With solutions and support from TeskaLabs, O2 will offer a POS service unmatched in quality that provides high-end application security, monitoring and real-time incident response. This gives O2 a significant marketing advantage over their competitors.
Contact us if you have any questions about monitoring electronic evidence of sales. One of our specialists will be more than happy to answer them for you.